Risk Maturity Scorer
Our online based detailed security risk assessment tool is designed to help organizations identify, evaluate, and prioritize potential security risks. The tool collects information on an organization such as its asset types, organizational structure, compliance needs, physical security requirements, etc. The assessment results are then used to prioritize and plan security initiatives, implement security controls, and monitor progress over time. Free risk assessment - http://airius.com/free-risk-maturity-evaluation/
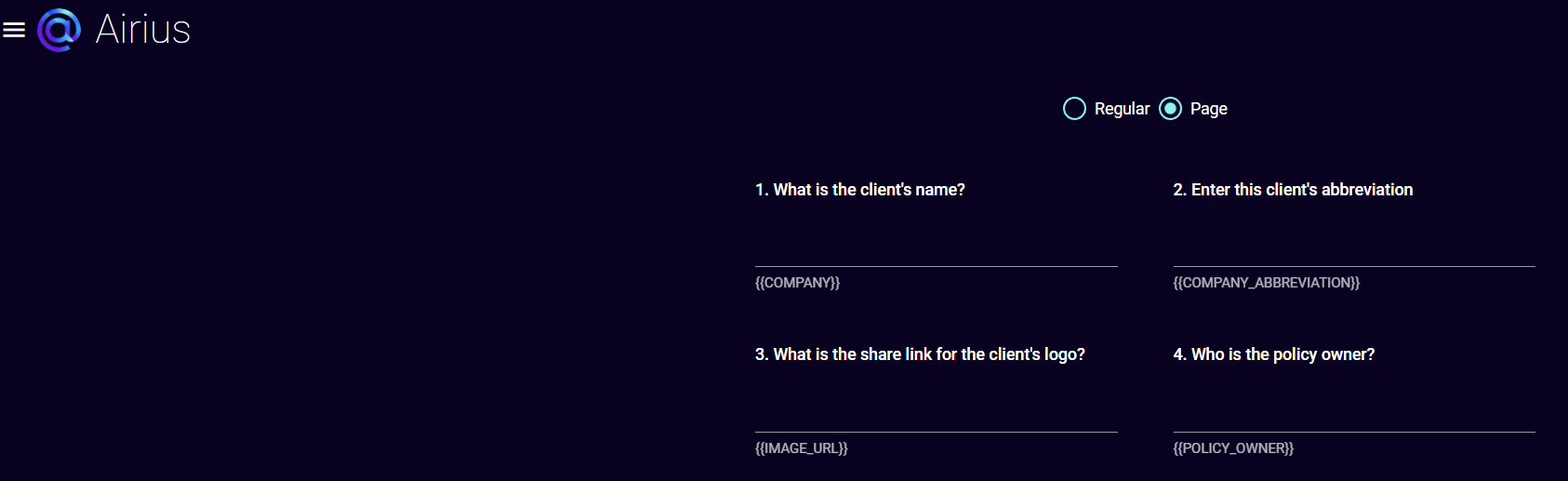
Policy Document Generation Tool for Customized Policies within Two Business Days
In conjunction with our Risk Management Framework service for our clients we host and maintain non-website policy related documents to rapidly generate and continually update such documentation as a subscription which is unique to the industry. This saves potentially hundreds of hours of internal labor to develop. We offer an easy to use interface for starting the process.
This includes creating the required policy and procedure documentation for:
ISO27001
ISO27002
SOC2 Type 2
NIST 800-53 R5
NIST CSF
CMMC (Level 2 and Level 3)
PCI DSS v3.2 and 4.0
For website related policies we partner with Termly to provide customized privacy policies, terms of use, cookie policy, and GDPR consent banners also within 2 business days.

GRC/IRM
We do custom integrations with GRC tools, network security tools, vulnerability scanning tools, endpoint protection tools, software code scanners, email configuration checkers, policy documents etc for a unified and single pane of glass view of risk.
Privacy Defense (Databroker Cleanup, Dark Web Monitoring, Privacy Management for Executives)
The privacy defense and reputation infrastructure is utilized to gain insight across open, deep, and dark web to look for potentially exposed intellectual property and personal information that has been leaked from organizations. We offer the ability through both the portal and an API to remove personal information of staff members from ~200 data brokers. This is commonly used for doxing and targeted phishing attacks. In addition, criminal groups often utilize the dark web to share compromised credentials and can be an indication of the threats to the organization before they become incidents which we regularly automatically monitor. Once we have the necessary staff information there is no configuration required by customers and is set up for each customer’s organization’s environment and assets.